Agriculture is perhaps not recognized as a sector that could be the target of hackers however this sector is now relying on increased connectivity and communication on-line and with this comes the threat of possible cyber attacks.
The Farming community has varied experience in protecting its IT and limited experience in the management of these types of risks.
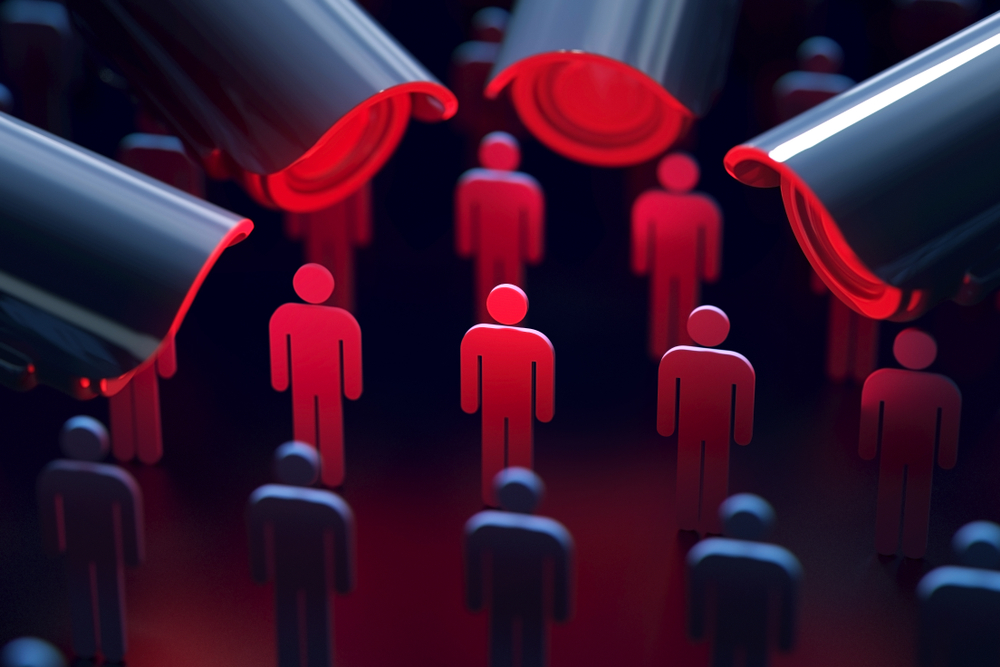
Cyber Threats
- Increased reliance on digitization and conversion from older computer systems
- Working with a broad number of suppliers increases supply chain threats
- Farm database being subject to a data breach from a hacker
- Loss of productivity as a result of a cyber attack impacting on yields
- Loss of storage facilities
- Compromise of farm management and logistics software
- Agricultural vehicle attacks
The Smart Factor
Agriculture is becoming more reliant on smart technology as this is cost effective and works effectively in this sector where movement of goods and animals dominants.
For example this involves some of the following :-
1.Livestock tracking wearables
2 Food tracking
3.Smart agriculture sensors for soil moisture and weather stations
Cyber Risk Management
Agriculture is linked to the food industry and any compromise in technology is going to have a very significant impact of the food supply chain , protection of this is vital. The food sector is classified as part of the 13 sectors that fall under Critical National Infrastructure (CNI), the prominence of this therefore is at the highest level. The management of risks in this sector should be a priority.
We have not seen many cyber attacks in this sector and it is maybe the case that few have been reported or they have been in significant to be reported.
Cyber Insurance
This is relatively new form of insurance and is now being purchased by many businesses in many different sectors and it is conceivable that the farming sector will also consider this with cyber risk becoming more relevant .
Image : Shutterstock